Clang 3.3 and Debian
Août 19th, 2013The LLVM toolchain version 3.3 has been released a couple months ago.
Here are now the result of the rebuild of Debian archive using this version of the compiler.
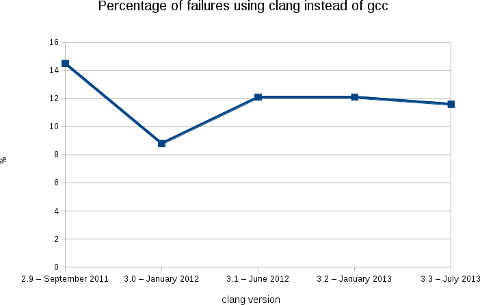
Like the previous releases, we are at a bit less than 12% of packages failing (2188 packages on a total of 18854).
More warnings / errors detections have been added to the software (for example: like this defect of the C++ standard or the detection of unused linker option) causing more build failures, but, in the mean time, we fixed some issues in the Debian packages...
As usual, the following image shows clearly the evolution of the build failures over time.
As stated in my blog post for the release 3.2, this rebuilds prove that Clang is ready for production in term of support of the C, C++ and Objective C languages.
With the performance results showed by Chandler Carruth from Google at the last Euro LLVM summit (see this video from 5:40), I believe that it is now time to report and fix the bugs in the upstream packages.
I also presented this work (video) at the Debconf 13 last week in Vaumarcus (Switzerland) and I will be also presenting this work at the Linux Plumbers Conference, New Orleans.
With Léo Cavaille (as part of his GSOC) and Paul Tagliamonte, we are also working on providing a better automatic rebuild infrastructure for clang-built packages (and other static analyzers). More in the next few weeks.
Finally, I would like to thank folks at AWS for the Debian credit and David Suarez for helping on with the Ruby segfaults.
Video of Debconf 13 available on the IRILL website
Août 19th, 2013While raw videos of the previous Debconf are available on:
http://video.debian.net/
We, at IRILL, are glad to provide a nice HTML5 interface (and flash if HTML5 videos are not available) to browse all the videos of Debconf 13:
http://www.irill.org/videos/debconf13
Merchandising at Debconf
Août 12th, 2013Debian France and Debian Swiss associations are now selling products at Debconf.
We are now selling
| Buff | 23 CHF / 18 euros | |
| Black polo | 31 CHF / 25 euros | |
| Rugby polo | 50 CHF / 40 euros | |
| Mousepad | 13 CHF / 10 euros |
We have also some new hoodies.
They come in 4 colors: black, white, grey and dark blue.
With or without zip:
Without zip: 44 CHF / 35 euros
With zip: 50 CHF / 40 euros
With also have hats:
Price: 10 CHF / 9 euros
We have also the Debian umbrellas and knifes.
For those who are at Debconf, they are for sell at the Debconf front desk from 4 to 6 and will be probably available for sell on enventelibre after the event.
Switch to OpenJDK 7
Août 5th, 2013As announcement on debian-devel-announce, I just uploaded java-common version 0.49. This version changes the default version of OpenJDK to version 7.
That means that packages depending on default-jdk/default-jre will be now built with OpenJDK 7 (instead of the 6) and also that the java/javac commands will be providing Java 7.
I also used the opportunity of this upload to update the Java policy.
LLVM toolchain packages
Juillet 7th, 2013In parallel of my work on the LLVM Debian/Ubuntu nightly packages, I uploaded a couple months ago the same packages for the stable releases of the LLVM toolchain. By toolchain, this means LLVM + Clang + Clang extra tools + compiler-rt + polly + LLDB.
Previously, they were packaged as separate source packages. Making the maintenance harder and, especially, limiting the packaging of LLDB and polly.
Currently, we have in the archive:
LLVM toolchain 3.2 (note that LLDB is disabled from this release).
For the 3.2 release, I am planning to focus on RC bug fixes.
The 3.3 and snapshot releases will get the feature improvements.
llvm-default will point to the 3.3 release once it builds on all architectures and it reached testing aka Jessie (probably during summer).